| Affected plugin | SiteGround Security |
| Active installs | 600,000+ |
| Vulnerable version | <= 1.3.0 |
| Audited version | 1.3.0 |
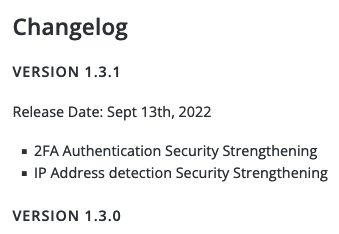
| Fully patched version | 1.3.1 |
| Recommended remediation | Upgrade to version 1.3.1 or higher |
Description
The plugin is vulnerable to IP spoofing, which an attacker can abuse the perform a DOS attack on the target site by preventing legitimate users, or the site’s reverse proxy from making requests to the wp-login endpoint.
Alternatively, an attacker can spoof his IP address to bypass all rate-limit restrictions.
Proof of concept
The plugin uses the Helper::get_current_user_ip method everywhere it needs access to the current request’s IP address.
The method looks like this:
public static function get_current_user_ip() {
$keys = array(
'HTTP_CLIENT_IP',
'HTTP_X_FORWARDED_FOR',
'HTTP_X_FORWARDED',
'HTTP_X_CLUSTER_CLIENT_IP',
'HTTP_FORWARDED_FOR',
'HTTP_FORWARDED',
'REMOTE_ADDR',
);
foreach ( $keys as $key ) {
// Bail if the key doesn't exists.
if ( ! isset( $_SERVER[ $key ] ) ) {
continue;
}
// Bail if the IP is not valid.
if ( ! filter_var( $_SERVER[ $key ], FILTER_VALIDATE_IP ) ) { //phpcs:ignore
continue;
}
return preg_replace( '/^::1$/', '127.0.0.1', $_SERVER[ $key ] ); //phpcs:ignore
}
// Return the local IP by default.
return '127.0.0.1';
}Each HTTP header stored in the “$keys” variable is attacker-controlled and can be trivially spoofed.
curl -X POST https://target.com/wp-login.php -d "log=bogus" -d "pwd=bogus" -H "Client-IP: 39.213.207.22"The request above will register a rate-limit hit for IP address 39.213.207.22.
Proposed patch
This is described in great length in this article of us.
Summary: Only ever use REMOTE_ADDR to access to current IP.
Timeline
| Vendor contacted | September 07, 2022 |
| First Response | September 12, 2022 |
| Fully patched at | September 13, 2022 |
| Publicly disclosed | April 24, 2023 |
Miscellaneous
- The vendor fixed the vulnerability promptly but did not disclose in his release notes that users must update as soon as possible.
Leave a Reply